Maimon David (39 results)
Search filters
Product Type
- All Product Types
- Books (39)
- Magazines & Periodicals (No further results match this refinement)
- Comics (No further results match this refinement)
- Sheet Music (No further results match this refinement)
- Art, Prints & Posters (No further results match this refinement)
- Photographs (No further results match this refinement)
- Maps (No further results match this refinement)
- Manuscripts & Paper Collectibles (No further results match this refinement)
Condition Learn more
- New (28)
- As New, Fine or Near Fine (7)
- Very Good or Good (2)
- Fair or Poor (No further results match this refinement)
- As Described (2)
Binding
Collectible Attributes
- First Edition (1)
- Signed (No further results match this refinement)
- Dust Jacket (1)
- Seller-Supplied Images (11)
- Not Print on Demand (37)
Language (3)
Free Shipping
Seller Location
Seller Rating
-
Writing in the Academic Disciplines : A Curricular History
Language: English
Published by Southern Illinois University Press, 2002
ISBN 10: 0809324679 ISBN 13: 9780809324675
Seller: GreatBookPrices, Columbia, MD, U.S.A.
Condition: New.
-
Writing in the Academic Disciplines : A Curricular History
Language: English
Published by Southern Illinois University Press, 2002
ISBN 10: 0809324679 ISBN 13: 9780809324675
Seller: GreatBookPrices, Columbia, MD, U.S.A.
Condition: As New. Unread book in perfect condition.
-
Writing in the Academic Disciplines A Curricular History
Language: English
Published by Southern Illinois Univ Pr, 2002
ISBN 10: 0809324679 ISBN 13: 9780809324675
Seller: Revaluation Books, Exeter, United Kingdom
Paperback. Condition: Brand New. 2nd sub edition. 410 pages. 8.25x5.25x1.00 inches. In Stock.
-
Writing in the Academic Disciplines : A Curricular History
Language: English
Published by Southern Illinois University Press, 2002
ISBN 10: 0809324679 ISBN 13: 9780809324675
Seller: GreatBookPricesUK, Woodford Green, United Kingdom
Condition: New.
-
Writing in the Academic Disciplines : A Curricular History
Language: English
Published by Southern Illinois University Press, 2002
ISBN 10: 0809324679 ISBN 13: 9780809324675
Seller: GreatBookPricesUK, Woodford Green, United Kingdom
Condition: As New. Unread book in perfect condition.
-
Evidence-based Cybersecurity : Foundations, Research and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPrices, Columbia, MD, U.S.A.
Condition: As New. Unread book in perfect condition.
-
Hardcover. Condition: Very Good. No Jacket. May have limited writing in cover pages. Pages are unmarked. ~ ThriftBooks: Read More, Spend Less.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Majestic Books, Hounslow, United Kingdom
Condition: New. pages cm.
-
Evidence-based Cybersecurity : Foundations, Research and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPrices, Columbia, MD, U.S.A.
Condition: New.
-
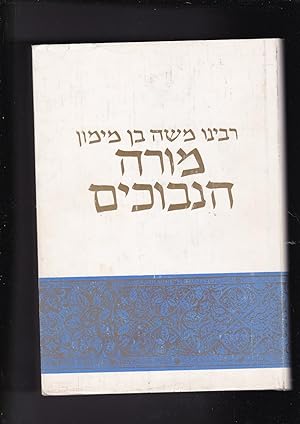
More Nevuchim More Hanevuchim
Language: Hebrew
Published by Mossad HaRav Kook, Jerusalem, Israel, 1984
Seller: Meir Turner, New York, NY, U.S.A.
Hardcover. Condition: Like New. Dust Jacket Condition: Very Good. In Hebrew. A new translation. 30, 2 plates, 445 pages.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Books Puddle, New York, NY, U.S.A.
Condition: New. pages cm First edition Includes bibliographical references and index.
-
Evidence-based Cybersecurity : Foundations, Research and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPricesUK, Woodford Green, United Kingdom
Condition: As New. Unread book in perfect condition.
-
Evidence-based Cybersecurity : Foundations, Research and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPricesUK, Woodford Green, United Kingdom
Condition: New.
-
Evidence-based Cybersecurity : Foundations, Research, and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPrices, Columbia, MD, U.S.A.
Condition: New.
-
Cybercrime Prevention: Theory and Applications (Crime Prevention and Security Management)
Book 33 of 37: Crime Prevention and Security ManagementLanguage: English
Published by Palgrave Pivot 2019-11-28, 2019
ISBN 10: 303031068X ISBN 13: 9783030310684
Seller: Chiron Media, Wallingford, United Kingdom
Hardcover. Condition: New.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Ria Christie Collections, Uxbridge, United Kingdom
� 59.57
� 11.98 shipping
Ships from United Kingdom to U.S.A.Quantity: Over 20 available
Add to basketCondition: New. In.
-
Evidence-based Cybersecurity : Foundations, Research, and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPrices, Columbia, MD, U.S.A.
Condition: As New. Unread book in perfect condition.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Biblios, Frankfurt am main, HESSE, Germany
Condition: New. pages cm.
-
Cybercrime Prevention: Theory and Applications (Crime Prevention and Security Management)
Book 33 of 37: Crime Prevention and Security ManagementSeller: Ria Christie Collections, Uxbridge, United Kingdom
� 60.59
� 11.98 shipping
Ships from United Kingdom to U.S.A.Quantity: Over 20 available
Add to basketCondition: New. In.
-
Evidence-based Cybersecurity : Foundations, Research, and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPricesUK, Woodford Green, United Kingdom
Condition: New.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Majestic Books, Hounslow, United Kingdom
Condition: New.
-
Condition: New.
-
Condition: New.
-
Evidence-Based Cybersecurity: Foundations, Research, and Practice (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipLanguage: English
Published by CRC Press 2022-06-21, 2022
ISBN 10: 1032062762 ISBN 13: 9781032062761
Seller: Chiron Media, Wallingford, United Kingdom
Hardcover. Condition: New.
-
Evidence-based Cybersecurity: Foundations, Research and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: Revaluation Books, Exeter, United Kingdom
Paperback. Condition: Brand New. 250 pages. 9.18x6.12x9.21 inches. In Stock.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Ria Christie Collections, Uxbridge, United Kingdom
� 72.78
� 11.98 shipping
Ships from United Kingdom to U.S.A.Quantity: Over 20 available
Add to basketCondition: New. In.
-
Evidence-based Cybersecurity : Foundations, Research, and Practice
Book 51 of 90: Security, Audit and LeadershipSeller: GreatBookPricesUK, Woodford Green, United Kingdom
Condition: As New. Unread book in perfect condition.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Books Puddle, New York, NY, U.S.A.
Condition: New. 1st edition NO-PA16APR2015-KAP.
-
Evidence-Based Cybersecurity
Book 51 of 90: Security, Audit and LeadershipLanguage: English
Published by Taylor and Francis Ltd, GB, 2022
ISBN 10: 1032062762 ISBN 13: 9781032062761
Seller: Rarewaves.com USA, London, LONDO, United Kingdom
Hardback. Condition: New. The prevalence of cyber-dependent crimes and illegal activities that can only be performed using a computer, computer networks, or other forms of information communication technology has significantly increased during the last two decades in the USA and worldwide. As a result, cybersecurity scholars and practitioners have developed various tools and policies to reduce individuals' and organizations' risk of experiencing cyber-dependent crimes. However, although cybersecurity research and tools production efforts have increased substantially, very little attention has been devoted to identifying potential comprehensive interventions that consider both human and technical aspects of the local ecology within which these crimes emerge and persist. Moreover, it appears that rigorous scientific assessments of these technologies and policies "in the wild" have been dismissed in the process of encouraging innovation and marketing. Consequently, governmental organizations, public, and private companies allocate a considerable portion of their operations budgets to protecting their computer and internet infrastructures without understanding the effectiveness of various tools and policies in reducing the myriad of risks they face. Unfortunately, this practice may complicate organizational workflows and increase costs for government entities, businesses, and consumers. The success of the evidence-based approach in improving performance in a wide range of professions (for example, medicine, policing, and education) leads us to believe that an evidence-based cybersecurity approach is critical for improving cybersecurity efforts. This book seeks to explain the foundation of the evidence-based cybersecurity approach, review its relevance in the context of existing security tools and policies, and provide concrete examples of how adopting this approach could improve cybersecurity operations and guide policymakers' decision-making process. The evidence-based cybersecurity approach explained aims to support security professionals', policymakers', and individual computer users' decision-making regarding the deployment of security policies and tools by calling for rigorous scientific investigations of the effectiveness of these policies and mechanisms in achieving their goals to protect critical assets. This book illustrates how this approach provides an ideal framework for conceptualizing an interdisciplinary problem like cybersecurity because it stresses moving beyond decision-makers' political, financial, social, and personal experience backgrounds when adopting cybersecurity tools and policies. This approach is also a model in which policy decisions are made based on scientific research findings.
-
Evidence-Based Cybersecurity (Security, Audit and Leadership Series)
Book 51 of 90: Security, Audit and LeadershipSeller: Biblios, Frankfurt am main, HESSE, Germany
Condition: New.